VibroAuth
This project started with a question I find especially valuable in product work: what happens when the default interaction model is itself part of the security problem?
PIN entry on phones is usually treated as a solved pattern. But in public contexts, it is surprisingly easy to infer meaning from finger movement, layout familiarity, and visible feedback. I wanted to explore whether a more private interaction model could reduce that risk without making authentication feel impossibly heavy.
The result was VibroAuth, a non-visual, dynamically rearranged PIN entry concept that uses haptic patterns to privately communicate keypad meaning to the user while making shoulder surfing materially harder.
Challenge
Shoulder surfing is not only a visibility problem. It is an inference problem. Even if users move quickly, observers can often reconstruct intent from finger paths, standard keypad expectations, and visible confirmation cues. That means the default PIN flow carries a structural weakness in public settings.
Reframing the problem
I approached this as a systems problem instead of a keypad polish problem. The question became: what if users could privately infer the layout, while observers could no longer confidently infer the meaning of visible touches? That shift opened a more meaningful solution space than simply obscuring or randomizing digits on screen.
Key design decisions
The concept became credible because of a few deliberate decisions that balanced learnability and security rather than optimizing for one at the expense of the other.
- The keypad stays visible as a structure, but the numbers themselves are hidden.
- This reduces the chance that an observer can directly map touches to digits.
- Long-touching a key plays a haptic pattern that helps the user infer the keypad layout.
- The user receives private information without broadcasting it visually.
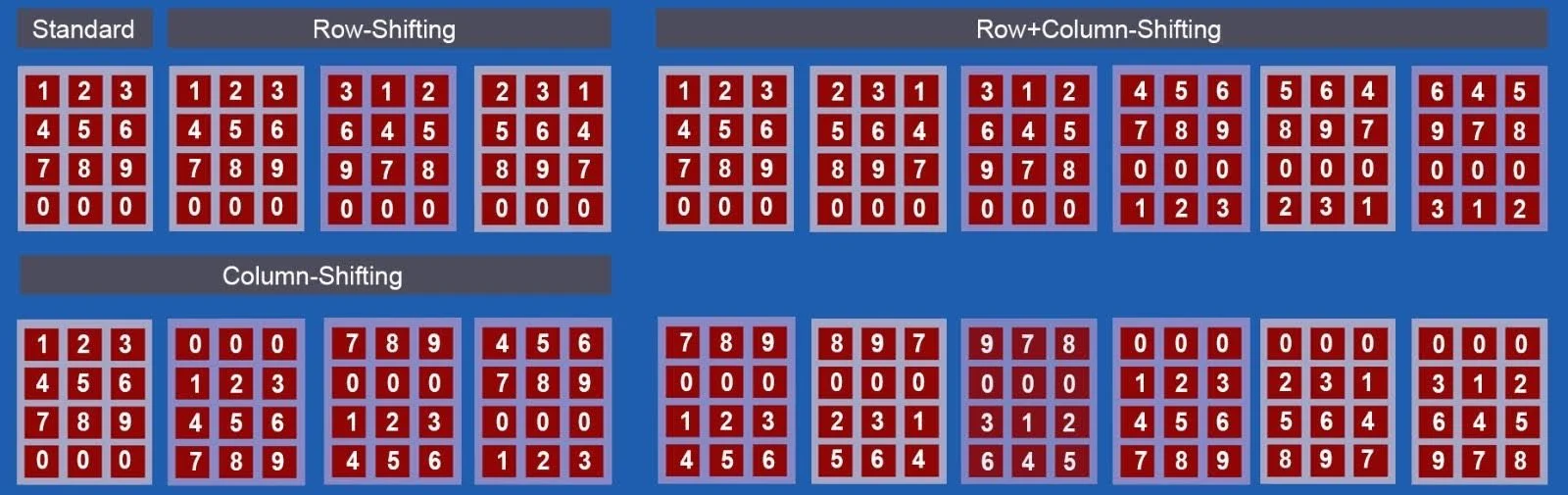
- Rows, columns, or both can shift instead of fully randomizing every digit.
- This preserves learnability while still expanding the attacker’s search space.
- Some variants shift again after each digit entry.
- This increases security significantly, but also increases effort and time.

Study design
I wanted the research to answer a product decision, not just validate a UI. The core question was: is this secure enough to matter, usable enough to learn, and practical enough to deploy in the right contexts?
- Participants first learned modified Morse-inspired haptic patterns for digits 0–9.
- They then used multiple authentication conditions across row-shifting, column-shifting, row+column shifting, and touch-shifting variants.
- Measures included recall accuracy, PIN entry accuracy, time, workload, and perceived security.
- A separate group observed authentication sessions and attempted to guess entered PINs.
- This tested whether the concept materially changed the attacker’s problem instead of only improving perceived privacy.






Impact
The findings pointed to a clear and nuanced product story: VibroAuth is not a universal replacement for standard unlock, but it is a strong candidate for contexts where the security gain justifies additional interaction cost.
- Participants learned the haptic patterns with 98.4% recall accuracy.
- Overall PIN entry accuracy was 94.6% across methods.
- Participants generally perceived the more dynamic methods as more secure.
- Touch-shifting variants reported zero successful attacks in the security study.
- The most secure methods also increased entry time, often to 10 seconds or more.
- Mental demand and effort rose as the layout became more dynamic.
- The concept is strongest in high-risk or high-sensitivity scenarios, not necessarily for every everyday unlock.





Reflection
This project is a strong representation of how I like to work as a designer and researcher. I am most useful when the problem is still underspecified, the constraints cut across multiple domains, and the team needs research that can shape a product decision rather than simply describe user pain.
- Design secure modes as context-aware options, not one-size-fits-all defaults.
- Allow users to calibrate haptic timing and intensity to fit device hardware and personal sensitivity.
- Explore more accessible variants for low-vision and blind users without relying on visible layout references.
- It shows strategic problem framing, not just UI execution.
- It demonstrates systems thinking across interaction, security, and user cognition.
- It produces a nuanced product recommendation grounded in evidence.
